REUTERS/Rick Wilking
Seventeen fake cellphone towers were discovered across the U.S. last week, according to a report in Popular Science.
Rather than offering you
cellphone service, the towers appear to be connecting to nearby phones,
bypassing their encryption, and either tapping calls or reading texts.
Les Goldsmith, the CEO of ESD America, used ESD's CryptoPhone 500 to detect 17 bogus cellphone towers. ESD is a leading American defense and law enforcement technology provider based in Las Vegas.
With most phones, these fake communication towers are undetectable. But not for the CryptoPhone 500, a customized Android device that is disguised as a Samsung Galaxy S III but has highly advanced encryption.
Goldsmith told Popular Science: "
Interceptor use in the U.S. is much higher than people had anticipated.
One of our customers took a road trip from Florida to North Carolina
and he found eight different interceptors on that trip. We even found
one at South Point Casino in Las Vegas.”
The towers were found in July, but the report implied that there may have been more out there.
Although it is unclear who owns the towers, ESD found that several of them were located near U.S. military bases.
"Whose interceptor is it? Who
are they, that's listening to calls around military bases? Is it just
the U.S. military, or are they foreign governments doing it? The point
is: we don't really know whose they are," Goldsmith said to Popular Science.
It's probably not the NSA — that agency can tap all it wants without the need for bogus towers, VentureBeat reported:
Not the NSA, cloud security
firm SilverSky CTO/SVP Andrew Jaquith told us. “The NSA doesn’t need a
fake tower,” he said. “They can just go to the carrier” to tap your
line.
ComputerWorld points out that the fake towers give themselves away by crushing down the performance of your phone from 4G to 2G while the intercept is taking place.
So if you see your phone operating on a slow download signal while
you're near a military base ... maybe make that call from somewhere
else.
In an amazing coincidence, police departments in a handful of U.S. cities have been operating "Stingray" or "Hailstorm" towers,
which — you guessed it — conduct surveillance on mobile phone activity.
They do that by jamming mobile phone signals, forcing phones to drop
down from 4G and 3G network bands to the older, more insecure 2G band.Impostor Cell Phone Towers Could Be Controlling Your Mobile
 Expand
Expand
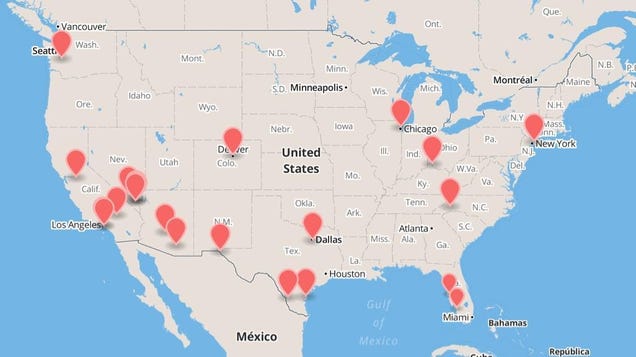
This
map shows the locations of 17 mysterious cell towers in the United
States that aren't part of any known cell phone provider network. Nobody
knows where they came from, but they are busily intercepting the
communications of any mobile in signal range. What happens next probably
isn't good.
Over at Popular Science,
Andrew Rosenblum has a story about this hidden network of cell phone
interceptors that could be snooping on your phone, and even installing
malware on it. Rosenblum talked to Les Goldsmith, maker of a secure
phone called CryptoPhone, who discovered at least 17 of these
"interceptor" towers in the United States. They seem to exist purely to
gain access to as many phones in range as possible.
Writes Rosenblum:
He points me to a map that he and his customers have created, indicating 17 different phony cell towers known as "interceptors," detected by the CryptoPhone 500 around the United States during the month of July alone ... Interceptors look to a typical phone like an ordinary tower. Once the phone connects with the interceptor, a variety of "over-the-air" attacks become possible, from eavesdropping on calls and texts to pushing spyware to the device."Interceptor use in the U.S. is much higher than people had anticipated," Goldsmith says. "One of our customers took a road trip from Florida to North Carolina and he found 8 different interceptors on that trip. We even found one at South Point Casino in Las Vegas."Who is running these interceptors and what are they doing with the calls? Goldsmith says we can't be sure, but he has his suspicions."What we find suspicious is that a lot of these interceptors are right on top of U.S. military bases. So we begin to wonder – are some of them U.S. government interceptors? Or are some of them Chinese interceptors?" says Goldsmith. "Whose interceptor is it? Who are they, that's listening to calls around military bases? Is it just the U.S. military, or are they foreign governments doing it? The point is: we don't really know whose they are."
Goldsmith
admitted later that it's unlikely that a government agency like the NSA
would do something like this, because they can simply go to the service
providers themselves and get the data they want. Indeed, in 2006 a
whistleblower at AT&T revealed that the NSA had a "secret room" at
the company's San Francisco facility where it was snooping on every piece of data that traveled over the network. So the security agency would hardly need one of these interceptors.
The
question is, who does? Anyone who is intercepting your phone
communications can do a lot more than listen in on phone calls or texts.
They can install a program that gains full access to the data stored on
your phone, and even converting your mobile into an eavesdropping
device that listens to what you're doing even when you think the phone
is turned off.


No comments:
Post a Comment